Cybersecurity researchers have disclosed three security flaws in the Rack Ruby web server interface that, if successfully exploited, could enable attackers to gain unauthorized access to files, inject malicious data, and tamper with logs under certain conditions.
The vulnerabilities, flagged by cybersecurity vendor OPSWAT, are listed below –
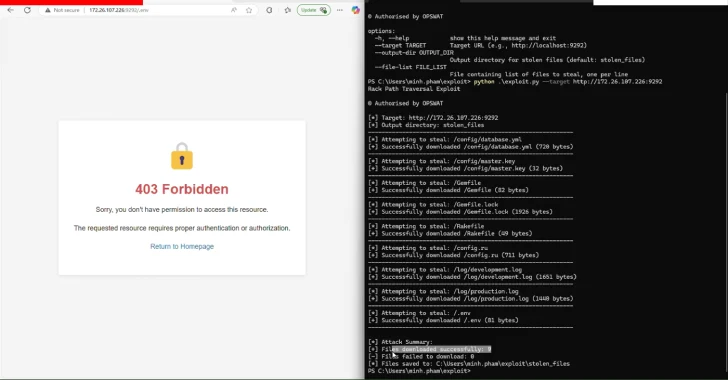
CVE-2025-27610 (CVSS score: 7.5) – A path traversal vulnerability that could be used to gain access to all files under the specified root: directory, assuming an attacker can determine the paths to those files
CVE-2025-27111 (CVSS score: 6.9) – An improper neutralization of carriage return line feeds (CRLF) sequences and improper output neutralization for logs vulnerability that could be used to manipulate log entries and distort log files
CVE-2025-25184 (CVSS score: 5.7) – An improper neutralization of carriage return line feeds (CRLF) sequences and improper output neutralization for logs vulnerability that could be used to manipulate log entries and inject malicious data
Successful exploitation of the flaws could permit an attacker to obscure attack traces, read arbitrary files, and inject malicious code.

“Among these vulnerabilities, CVE-2025-27610 is particularly severe, as it could enable unauthenticated attackers to retrieve sensitive information, including configuration files, credentials, and confidential data, thereby leading to data breaches,” OPSWAT said in a report shared with The Hacker News.
The shortcoming stems from the fact that Rack::Static, a middleware that’s used to serve static content like JavaScript, stylesheets, and images, does not sanitize user-supplied paths before serving files, leading to a scenario where an attacker can provide a specially crafted path to access files outside of the static file directory.
“Specifically, when the :root parameter is not explicitly defined, Rack defaults this value to the current working directory by assigning it the value of Dir.pwd, implicitly designating it as the web root directory for the Rack application,” OPSWAT said.
As a result, if the :root option is either undefined or misconfigured relative to the :urls option, an unauthenticated attacker could weaponize CVE-2025-27610 through path traversal techniques to access sensitive files outside the intended web directory.
To mitigate the risk posed by the flaw, it’s advised to update to the latest version. If immediate patching is not an option, it’s recommended to remove usage of Rack::Static, or ensure that root: points at a directory path that only contains files that should be accessed publicly.
Critical Flaw in Infodraw Media Relay Service
The disclosure comes as a critical security defect has been unearthed in the Infodraw Media Relay Service (MRS) that allows reading or deletion of arbitrary files via a path traversal vulnerability (CVE-2025-43928, CVSS score: 9.8) in the username parameter in the login page of the system.
Infodraw is an Israeli maker of mobile video surveillance solutions that are used to transmit audio, video, and GPS data over telecommunications networks. According to the company’s website, its devices are used by law enforcement, private investigations, fleet management, and public transport in many countries.

“A trivial Path Traversal vulnerability allows it to read out any file from systems for unauthenticated attackers,” security researcher Tim Philipp Schäfers said in a statement shared with The Hacker News. “Furthermore an ‘Arbitrary File Deletion Vulnerability’ exists that allows attackers to delete any file from the system.”
The flaw, which enables login with a username like “../../../../,” affects both Windows and Linux versions of MRS. That said, the flaw continues to remain unpatched. Vulnerable systems in Belgium and Luxembourg have been taken offline following responsible disclosure.
“Affected organizations are primarily advised to take the application offline immediately (since, despite early warnings, no manufacturer patch is available, and it is considered possible that the vulnerability will be exploited by malicious actors in the near future),” Philipp Schäfers said.
“If this is not possible, systems should be further protected with additional measures (such as using a VPN or specific IP unlocking).”